
Your digital identity is more than just a set of login credentials; it's the shadow that trails your every online move, tracking information about who you are and what you say and do, when, where, how often, and with whom.
Think about your day and how plugged in you are: first thing in the morning, you check the news on your phone or tablet, catch up on emails, and review your agenda while taking a sip of coffee before diving into work.
During working hours, your digital presence heightens —virtual meetings, Teams chats, file accessing, and even managing your finances online. Even on breaks, your virtual self doesn’t stop; you scroll through social media, exchange messages with friends and family, and perhaps indulge in some online shopping therapy on Amazon.
It's the same for small and medium-sized businesses. When SMBs operate in an increasingly digital landscape, identity protection isn't just a best practice—it's a must for ensuring the safety and integrity of your operations.
Because, you know who's always online too? Cybercriminals. And they are becoming more sophisticated. They leverage AI, buy passwords on the dark web (yes, that’s a whole industry on its own!), and their tactics are much more convincing and discreet.
In this interconnected world, everything is online, and without the right measures, everything can be breached.
Just using antivirus, anti-phishing tools, a strong password, and locking your screen isn't sufficient for protecting yourself. There is so much more that you can and should be doing, and the next crucial step is identity protection.
This article explains why identity protection is important for small businesses and provides tips on how to protect your identity.
What is Identity Protection
Identity protection or digital identity security is about keeping your personal information safe online. It includes steps taken to prevent unauthorized access, fraud, or misuse of your digital identity.
In essence, digital identity protection involves the proactive steps taken to prevent sensitive information, such as personal data and login credentials, from falling into the wrong hands.
Not only is it about your digital identity, but it also goes into protecting the devices linked to your credentials (tablets, smartphones, laptops, or computers) and the sensitive data and privacy of others, including your customers, partners and coworkers.
Importance of Identity Security
Cybercriminals aren't merely looking to mimic you; they're after the advantages that come with possessing your credentials. Cloud identity security is crucial and goes beyond protecting your reputation, it’s also a proactive way to secure the devices associated with your credentials (computers, smartphones, networks, etc.) and other people’s sensitive data and privacy, such as your customers', partners’, and coworkers' information.
With your ID someone can gain access to your company's confidential financial records to manipulate critical decision-making documents and infiltrate your enterprise’s network. They can install malicious software that not only steals sensitive data but also disrupts essential operations—all under your authority and responsibility.
Having said that, let’s look at some of the main reasons why deploying and monitoring identity security measures is important:
- SMB Data Breaches Are on the Rise:
.jpg?width=1024&height=500&name=why%20cybercriminals%20attack%20SMBs%20(2).jpg)
SMBs are increasingly becoming targets for cybercriminals due to their perceived vulnerability. Because SMBs typically have fewer resources: time, IT support, IT knowledge, advanced security procedures, employee training, and limited cybersecurity budgets, attackers see them as an easy heist.
And, an attacker might look at your organization as an easy entry point to harm bigger companies. Even if you're not the main prize, you could still get hit with collateral damage. So, better believe, slacking on identity protection is just asking for trouble in the wild world of the cloud.
- Prevent Financial Implications:
The aftermath of a security breach can be financially crippling for SMBs. Costs associated with regulatory fines, legal actions, and the expenses required to restore compromised systems can be overwhelming. It’s wiser to invest in cloud identity security as a preventive method.
- Maintain Customer Trust and Reputation:
.jpg?width=1024&height=500&name=reputational%20damage%20of%20a%20security%20breach%20(1).jpg)
Your organization thrives on building trust with your customer base and your stakeholders. When your reputation gets a hit, it's like a leaky faucet that slowly drips away potential deals. People remember the stains more than the shine, and in a world where connections matter, a tarnished rep means fewer handshakes and more closed doors.
So, safeguard that image because in the end, a scarred reputation doesn't just hurt feelings; it hurts your business bottom line.
- Identity Security is Key to Achieve Compliance:
Identity security and access management plays a pivotal role in regulatory compliance, aligning with the stringent standards set to protect user data.
Identity is a key component of the Zero Trust model. In this model, identities (representing people, services, etc.) control access to data. Before an identity attempts to access a resource, organizations must verify the identity with strong authentication, ensure access is compliant and typical for that identity, and follow least privilege access principles.
Once the identity has been verified, access to resources can be controlled based on organizational policies, on-going risk analysis, and other tools.
- Bolster Productivity:
.jpg?width=1024&height=500&name=forgotten%20password%20ticket%20(1).jpg)
The ripple effect of identity security extends to operational efficiency, manifesting as a reduction in IT operational costs and time investment. With fewer password-related problems, IT professionals can redirect their efforts to strategic initiatives, optimizing workflows and resulting in tangible cost savings for organizations. This improves user experience (UX) and prevents fatigue.
It’s 2024, and just as cybercriminals have advanced tech and schemes, you should upgrade your defenses too. Default email security alone won’t stand the ground against these new threats. If you want to stay ahead of the game, invest in identity security.
How to Protect Your Digital Identity
Now that we understand the significance of identity protection for SMBs, let's explore practical ways to secure your digital identity:
-
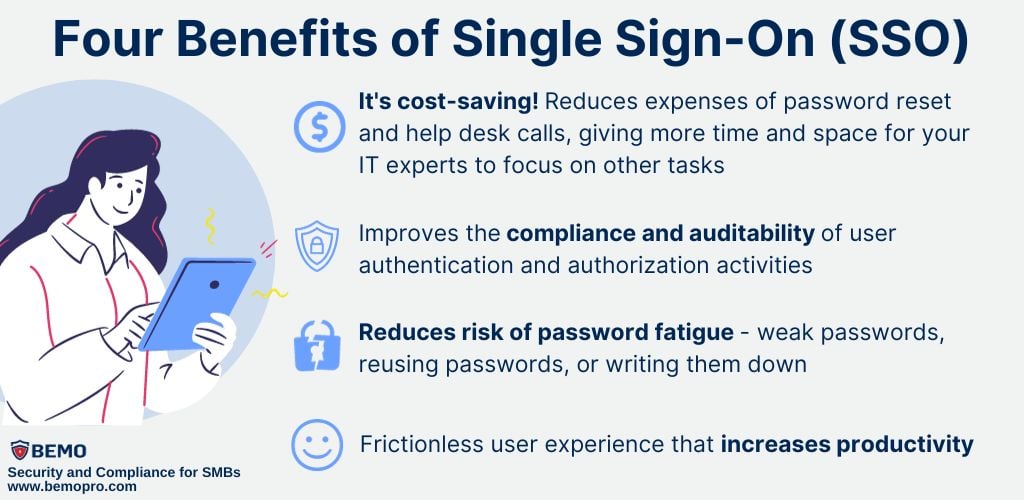
Single Sign-on:
Single Sign-On is a system that allows users to authenticate themselves just once and then be granted access to multiple applications or systems without having to log in again.
This is how it works: when the user signs in, SSO securely stores their authentication information in a central location. Later, when the user wants to access a different application or system, the SSO system automatically sends the stored authentication information, eliminating the need for the user to re-enter their login credentials.
This makes your life easier, because workflows involving multiple credentials can be burdensome and result in people finding risky ways to avoid those extra steps to simply log in.
-
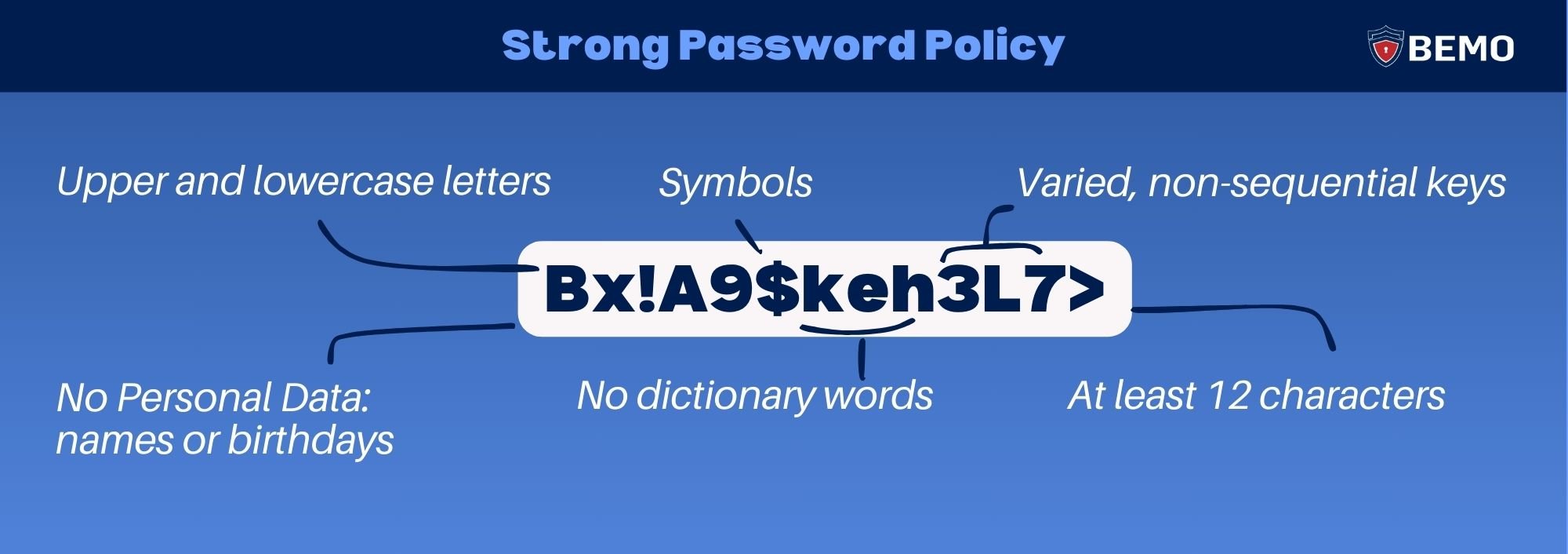
Password Policies:
Using unique passwords for each account, regularly updating them, and sticking to a strong password policy, prevents a security domino effect if one is compromised.
Consider using a reputable password manager for secure, randomized passwords, which are then stored in a secure, encrypted vault.
Also, since I'm on the password’s topic, I strongly advise deploying Self-Service Password Reset (SSPR). This service gives users the ability to change or reset their passwords with ZERO helpdesk or administrator involvement, making things easier for everyone. Your IT staff gets a break from those tickets, and your users can reset their own passwords securely in no time.
3. Conditional Access:
This feature allows you to control who can access your organization's resources and under whatconditions. It can be set up to allow regular sign-in when the user is on the corporate network or
a registered device but prompt additional verification factors when the user is remote or on a
personal device.
Conditional Access policies can also be set up to require MFA when risky sign-on situations are encountered, such as different locations, devices, or times than usual.
Conditional access gives you more control and flexibility over your company information and services. You can decide who can access them, when they can access them, and how they can access them.
4. Multifactor Authentication (MFA):
Multifactor authentication refers to using multiple methods of identity verification to allowaccess to users. Typically, in addition to a password, users must provide an extra authenticator
to reduce the risk of breach.
5. Continuous Monitoring:
In an era dominated by rapid technological advancements, the importance of cybersecuritymonitoring cannot be overstated. You can’t just deploy security controls; you need to have an
alerting system and a team dedicated to staying vigilant and fixing gaps proactively.
Monitoring for suspicious activities, such as unusual login patterns or unauthorized access attempts, allows for early detection and swift response.
At BEMO we take this step very seriously, for every one of our security solutions we include monitored security alerts, we stay up-to-date on Microsoft Feature Updates or New Solutions we validate them and reflect them in our BEMO tenant first to review our Managed Service Offerings and update all relevant policies that directly impact BEMO customers.
And for BEMO Managed IT customers, we take full responsibility, proactively handling all alert actions included in your security package. Interested? Check out our Monitoring and Alerting page here.
To Conclude...
Identity protection is not just a buzzword but a fundamental aspect of running a secure and successful SMB. By understanding what identity protection entails and implementing proactive measures, you can navigate the digital landscape with confidence, safeguarding your business’s digital identities and the trust of your customers.
As the saying goes, prevention is better than cure – especially when it comes to your core, your identity.
Have any comments? Write them down in the comments section, we love to read them!
Have any questions? Schedule a call with one of our cybersecurity experts or visit our cybersecurity solutions page to find the package that suits your business seamlessly.
Top 10 Posts
-
Windows 10 Pro vs Enterprise
-
Migrate From Gmail to Office 365: Step-By-Step Guide
-
Windows 10 Enterprise E3 vs E5: What's the Difference?
-
What are the 4 types of Microsoft Active Directory?
-
How to Migrate from GoDaddy to Office 365
-
Google Workspace to Office 365 Migration: A Step-by-Step Guide
-
How to Set Up Office 365 Advanced Threat Protection
-
10 Benefits of Microsoft Teams
-
Top 3 Reasons to Move From Google Drive to Microsoft OneDrive
-
How to remove Office 365 from GoDaddy (tips and tricks)
-2.png?width=1080&height=1080&name=Untitled%20design%20(5)-2.png)


.jpg?width=1024&height=500&name=how%20much%20does%20a%20data%20breach%20cost%20(2).jpg)
.jpg?width=1024&height=500&name=compliance%20solutions%20(3).jpg)
.png?width=1024&height=500&name=MFA%20(3).png)


Leave us a comment!