Many employees juggle a multitude of passwords for various accounts, applications, email, and computer logins. For them, the struggle lies in constantly recalling numerous passwords, leading to frequently having to rely on the 'forgot password' reset link. This proves to be not only just a time-consuming hassle, but also disrupts the flow of their work.
From an IT perspective, the issue amplifies as employees flood the department with password reset requests. If this situation resonates with you and leaves you feeling exasperated, you're not alone! It is a phenomenon known as password fatigue, and in this post, we'll delve into its intricacies, exploring the associated risks and, most importantly, offering solutions to alleviate this burden.
Join us as we discuss:
Password Fatigue
So, what exactly is password fatigue? Password fatigue is that exasperating feeling you get when you have to remember and manage many passwords for various online accounts and services, leading to mental exhaustion and frustration. .jpg?width=1024&height=500&name=what%20is%20password%20fatigue%20(1).jpg)
In understanding the roots of password fatigue, several factors come into play, each contributing to the mental burden users experience.
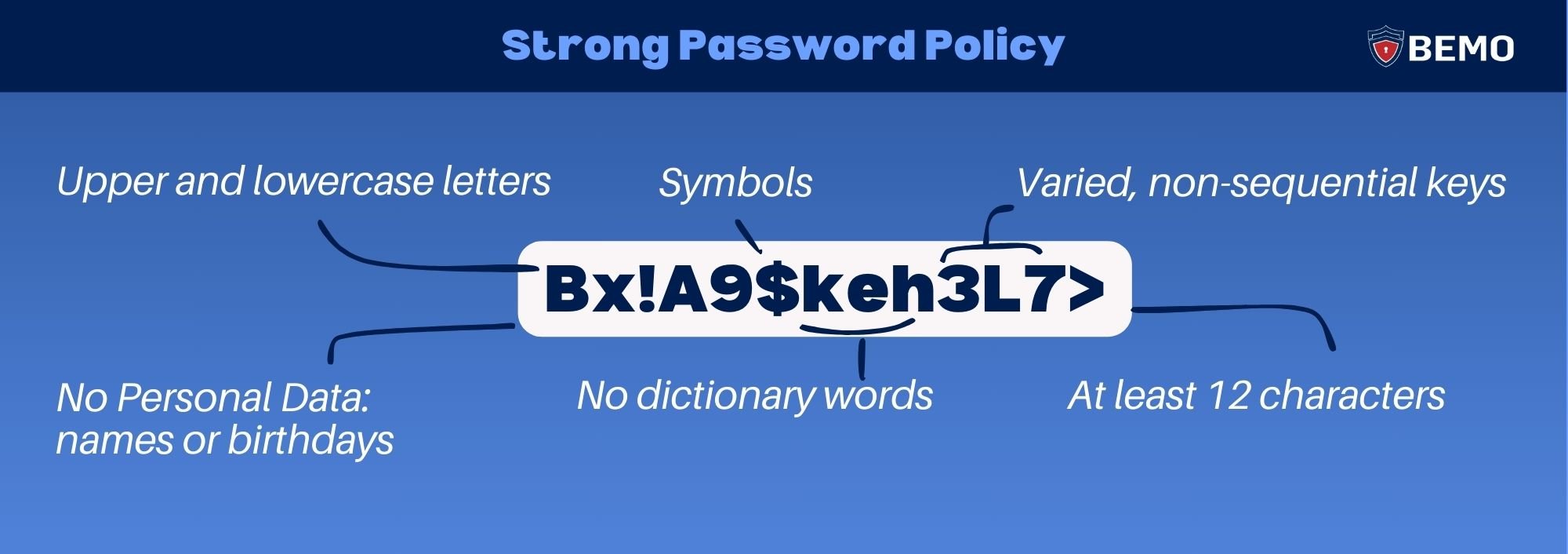
One significant factor is the imposition of complexity requirements by security protocols. These measures advocate for increasingly intricate passwords, demanding a combination of uppercase and lowercase letters, numbers, and symbols. Don’t get us wrong, a strong password is non-negotiable, but having to remember many elaborate combinations turns what should be a smooth sign in experience into a mentally exhausting task.
Just as you think you've mastered the art of password juggling, certain platforms throw a curveball, requiring a password refresh and resetting your progress. Frequent password changes try to enhance security by ensuring regularly updated credentials. However, if done too frequently they can be confusing and annoying.
The struggle is real, and it often leads to a cascade of emotions—anger, defeat, and the temptation to throw caution to the wind and resort to the same password for everything. Been there, done that? Well, you've experienced password fatigue. Now that you have a name for it, you're part of the club.
The bottom line is, as your digital presence expands, with numerous websites and applications requiring unique login credentials, it can be challenging to create and remember strong passwords for each one. Password fatigue underscores the need for better, more user-friendly authentication methods to enhance both security and user experience.
Risks of Password Fatigue
The repercussions of password fatigue extend beyond the mental strain and often manifest in risky behaviors that compromise overall security.
Fatigue may lead individuals to create simplistic and easy-to-remember passwords. Unfortunately, these are often also easy for hackers to guess, putting accounts at risk of unauthorized access.
Ever wondered "how secure is my password"? Maybe not as secure as you thought... click for a fun fact!
You’ll be shocked to know that over 90% of "easy-to-remember" passwords can be cracked in less than 6 hours!
On the other hand, one of the most significant dangers of password fatigue is the tendency to reuse passwords across multiple accounts.
They might meticulously craft what they believe to be a robust password yet opt for the ease of using this singular password across all their digital profiles.
The problem is, if one account is compromised, it opens a gateway to potential breaches in other accounts sharing the same credentials.
.jpg?width=1024&height=500&name=password%20reuse%20(1).jpg)
"That's not my case. Who does that now a days"? Click to check the stats on password reuse
Statistically speaking 80% of your employees reuse passwords!
To cope with the complexity of passwords, and try to prevent the two previously mentioned risks, some users resort to writing passwords down on paper or a digital sticky note. While it may seem like a practical solution, this practice introduces a significant security risk. If the information were to fall into the wrong hands, it could compromise the security of many accounts.
Moreover, this method doesn't tackle the frustration entirely, as users would still find themselves searching for the specific notepad or piece of paper containing the required password.
.png?width=1024&height=500&name=password%20managers%20(1).png)
"How bad can it be?" Click here to find out!
Writing down your passwords on sticky notes makes you 3 times more vulnerable to attacks!
How to Defend Against Password Fatigue
The good news is that there are ways to combat password fatigue. Let's discuss 4 tools to make your digital life a bit breezier!
Multifactor Authentication (MFA)
First up, we've got MFA. This tool adds an extra layer of security that doesn’t rely solely on passwords. It requires users to provide two or more verification factors to gain access. This could include something you know (password, pin), something you have (a smartphone for authentication codes), or something you are (biometric data like face recognition or fingerprint scanning).
This way, if a cybercriminal decodes your password, they won’t be able to do anything with it because they’ll lack the second form of verification (unless they trick you into providing the second form of authentication you have setup). 
Take the time to guarantee that your MFA system is optimized and user friendly; otherwise, you might trade password fatigue for MFA fatigue - a weariness induced by incessant requests for codes or various authentication methods. This can be stressful and tiring, and cybercriminals are aware of this and how to use it to bypass MFA and gain full access to your account.
Imagine an employee who needs to access multiple systems throughout the day, and each system requires a separate MFA authentication. The constant switching between devices or entering intricate codes can result in MFA fatigue.
Did you know that the average US smartphone user receives over 40 daily notifications? While most are legitimate, let’s say a cybercriminal decodes your password and sends multiple MFA requests to you. You might mistake it for a real request or simply get annoyed by the constant notifications and ultimately, approve it—a tactic known as MFA bombing or MFA fatigue attack.
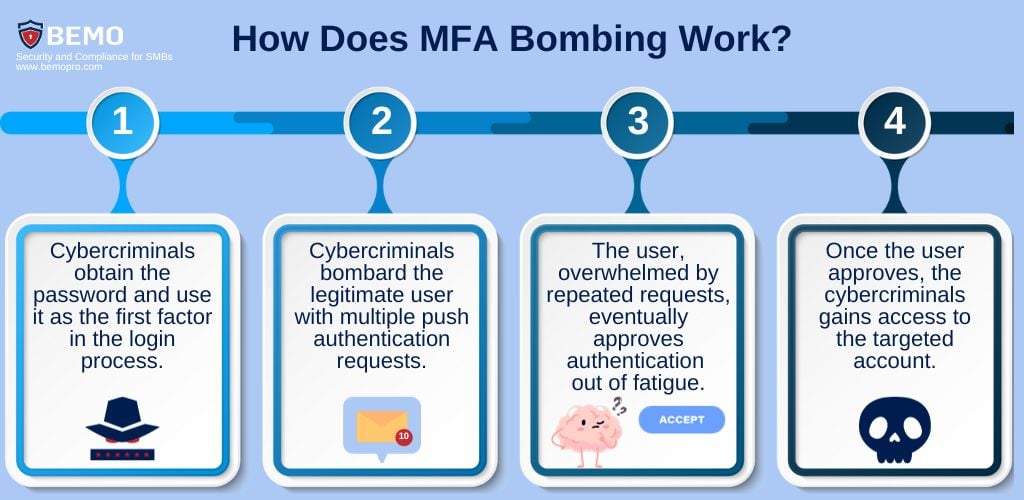
To combat an MFA fatigue attack, companies should implement best practices that balance security and usability, consider the following recommendations:
- Use one-time password (OTP) based MFA where possible, rather than MFA that uses one-click approval buttons. Additionally, it is recommended to apply additional context such as location and application to enhance awareness.
.png?width=710&height=347&name=authenticator%20app%20(1).png)
- Use identity systems that intelligently adapt the level of authentication based on user behavior and risk factors. It considers things such as location, devices, and login patterns.
Minimizing MFA prompts should also be a key consideration, and by implementing modern adaptive MFA, the second factor challenges are only surfaced under more risky scenarios, such as when an user logs in during unusual work hours.
- Use Conditional Access to ensure your systems can only be accessed on certain approved devices, approved locations or with certain login methods. For example, if a cybercriminal does gain access to your credentials through MFA bombing and is accessing from an external device or an unapproved location, they will be blocked.
Improve User Awareness by training employees about social engineering attacks like MFA Bombing. - Implement easy-to-use authentication methods, such as biometrics, push notifications, or Single Sign-On, which you will learn about in the following point.
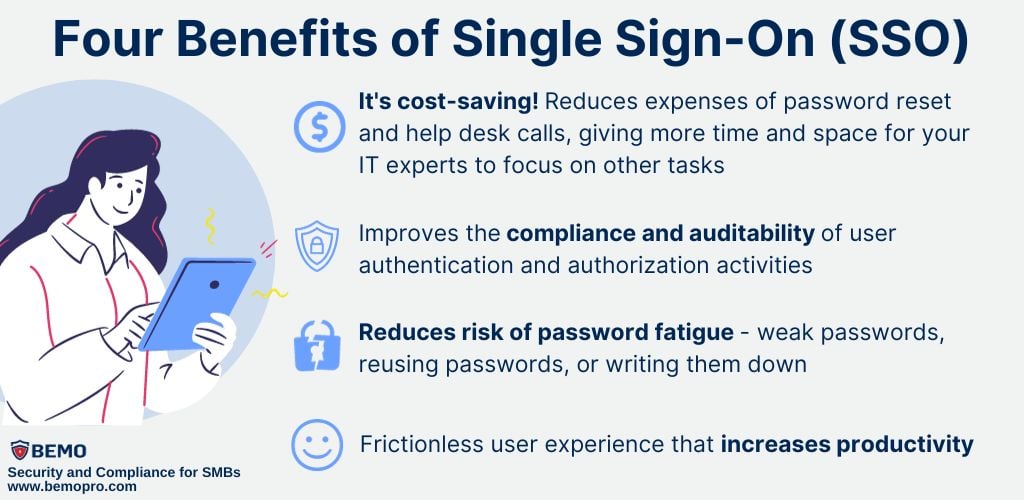
Single Sign-On (SSO)
With SSO, you only need to authenticate your credentials once to gain access to multiple systems or applications. This means you won't have to repeatedly go through the MFA process for each separate system.
SSO is NOT the same as reusing your passwords. Yes, with SSO you use a single set of credentials to access multiple applications or services. However, the key difference is that these credentials are not shared in the same way as when you reuse a password across various accounts.
In the case of SSO, a secure authentication mechanism is used to validate your identity, and a unique token or proof of authentication is exchanged with each application.
So, even though you're using one set of credentials for convenience, the underlying security is maintained because you're not actually sharing the same password across different platforms. If one account is compromised, it doesn't expose your credentials for other accounts connected via SSO.
Password-less Authentication
MFA makes user authentication much safer, but it does impact the user experience. MFA also leaves the vulnerable password as part of the equation. Password-less authentication is a form MFA that replaces the password part with a secure alternative. The goal is to eradicate password use and eliminate their value for attackers.
With Password-less Authentication technologies like Windows Hello, the Microsoft Authenticator app, and FIDO2 security keys, logging in becomes a snap. Biometrics like facial recognition or fingerprint scanning unlock cryptographic keys to securely allow sign-in – no password required!
Your IT team will thank you and your employees will feel like they work for a company on the cutting edge!
Password Manager
Picture this: a secure vault where all your passwords are encrypted and stored. You only need to remember one master password.
At BEMO we use Keeper to store our passwords and auto-fill our login credentials for all our sites. It even auto-generates new, iron-clad passwords for ones we've never used before.
We have an option for Keeper purchase as an add-on, available with all our Cybersecurity Plans. It is also included for free with Platinum.
To Conclude...
As we wrap up our exploration of password fatigue and its intricate challenges, it's clear that the struggle is real. The mental exhaustion, risky behaviors, and the temptation to take shortcuts are hurdles many of us face in the digital realm. But we hope this article has also given you actionable tips on practical solutions to fortify your online security and make your digital life more manageable.
At BEMO, we understand the complexities of navigating the digital landscape safely. If you're curious about deploying these solutions against password fatigue or exploring our cybersecurity deals that include cutting-edge identity security features, don't hesitate to reach out.
Our experts are ready to guide you toward a more secure and user-friendly online experience. Take the next step in fortifying your digital presence!
Top 10 Posts
-
Windows 10 Pro vs Enterprise
-
Migrate From Gmail to Office 365: Step-By-Step Guide
-
Windows 10 Enterprise E3 vs E5: What's the Difference?
-
What are the 4 types of Microsoft Active Directory?
-
How to Migrate from GoDaddy to Office 365
-
Google Workspace to Office 365 Migration: A Step-by-Step Guide
-
How to Set Up Office 365 Advanced Threat Protection
-
10 Benefits of Microsoft Teams
-
Top 3 Reasons to Move From Google Drive to Microsoft OneDrive
-
How to remove Office 365 from GoDaddy (tips and tricks)
-2.png?width=1080&height=1080&name=Untitled%20design%20(5)-2.png)




Leave us a comment!