In today's interconnected and data-driven world, safeguarding sensitive information has never been more critical. As businesses continue to rely on digital infrastructure to operate, the need for robust cybersecurity measures becomes increasingly apparent.
One way organizations can demonstrate their commitment to data security is by undergoing a SOC 2 compliance audit. In this blog post, we'll provide you with valuable tips to help you effectively prepare for a SOC 2 audit and maintain a culture of security and compliance readiness.
- Understanding SOC 2 Audits
- Tip 1: Build Out Your Security Tech Stack
- Tip 2: Build Your Compliance Team
- Tip 3: Gather Only the Necessary Documentation
- How BEMO Can Help
Understanding SOC 2 Audits:
An SOC 2 compliance audit is an assessment of an organization's controls and processes related to data security, availability, processing integrity, confidentiality, and privacy. It is performed by an independent third-party auditor and aims to ensure that a company's controls and evidence are aligned with the agreed-upon terms and expectations set by your customers to adequately protect sensitive customer and client data.
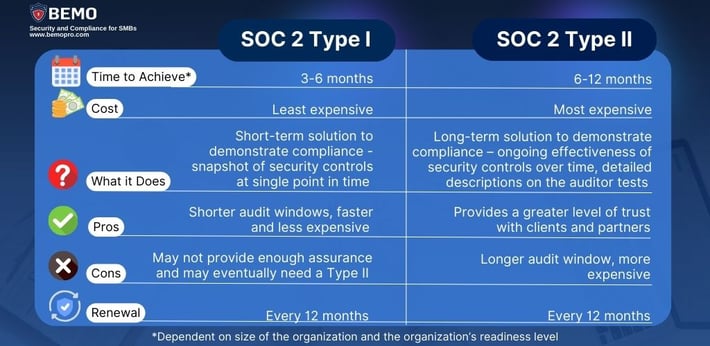
There are two common SOC 2 Audit flavors: Type 1 and Type 2.
- SOC 2 Type 1 Audit: This evaluates the design and implementation of controls at a specific point in time. It offers a snapshot of your organization's security posture at the moment of assessment.
- SOC 2 Type 2 Audit: In contrast, a Type 2 audit assesses the effectiveness and operationalization of these controls over a specified period (usually six months or more). This provides a more comprehensive evaluation of your organization's commitment to data security.
The choice between SOC 2 Type 1 and Type 2 depends on your business goals, budget, maturity and timeline constraints, as well as industry requirements. Make sure to read our blog post to determine which is the audit that you need.
Now that you have a clear overview of what SOC 2 is, let's delve into some actionable tips that will help you prepare for your audit.
Tip 1: Build Out Your Security Tech Stack
To kickstart your SOC 2 journey, we emphasize the importance of fortifying your organization's digital defenses by assembling a robust security technology stack. Here's a closer look at a few key components:
- Password Manager: A password manager is a software tool that securely stores and manages passwords for your organization. At BEMO our go-to password Manager choice is Keeper. It helps ensure that employees use strong, unique passwords for their accounts. This is crucial because weak or reused passwords are a common entry point for cyberattacks.
- Threat Detection and Response software: Antivirus and Antimalware software are necessities and must be kept up to date on all devices, including mobile devices. But basic antivirus isn’t enough. To achieve compliance, organizations need to implement advanced threat protection solutions that include endpoint detection and response (EDR) capabilities, stopping both known and unknown threats at the endpoint level. One such solution is Microsoft Defender for Endpoint, which not only provides next generation antivirus protection, but also EDR capabilities that can help organizations prevent, detect, and remediate cyberattacks in real time.
- Vulnerability Scanner: Vulnerability scanners automatically identify and assess vulnerabilities in your network and systems. Regular scanning helps you discover potential weaknesses before attackers can exploit them, allowing you to proactively address security issues.
- Background Check Provider: To ensure the integrity of your team, particularly those with access to sensitive data, consider using a reputable background check provider. This step helps mitigate insider threats and build trust with your clients and customers.
- Backup software: Backups are an essential strategy to ensure important data is protected from loss. Loss can occur as a result of things such as hardware failure, a malicious attack, natural disasters, or even accidental deletion. Backup processes and procedures are an integral part of your Disaster Recovery and Business Continuity Plans. The company must be able to prove that backups are not only being performed regularly, but also that backup data is secured, encrypted, and separated from the production environment. Backups must be tested regularly to verify the integrity of the backups.
Tip 2: Build Your Compliance Team
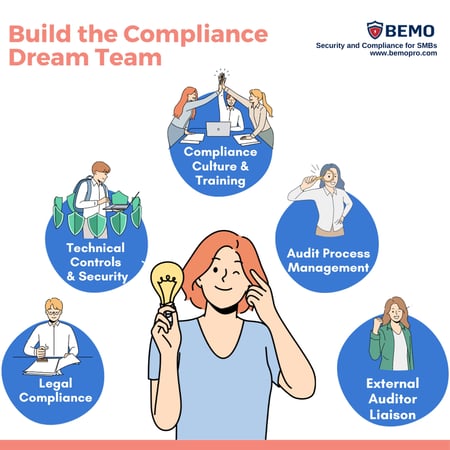
Preparing for an SOC 2 audit requires a coordinated effort. Building a compliance team ensures that you have an expert dedicated for each process and task.
Here's a breakdown of the roles within this team:
- Chief Compliance Officer (CCO): This individual takes overall responsibility for managing the audit process, coordinating team efforts, and liaising with external auditors.
- Project Manager: The project manager plays a crucial role in organizing and overseeing the audit preparations. They assign tasks, make sure that deadlines are met, and ensure documentation is in order.
- IT and Security Personnel: These experts focus on implementing and maintaining the technical controls required for SOC 2 compliance. They ensure that your systems and infrastructure are secure and meet audit standards.
- Legal Team: The legal team deals with contractual and legal aspects of compliance, ensuring that your organization's policies and practices align with legal requirements.
- Human Resources (HR) and Administrative Staff: Managing policies, training, and communication with employees is the responsibility of HR and administrative staff. They help create a culture of compliance awareness within the organization.
- External Consultant: In some cases, organizations may opt to bring in an external consultant with expertise in SOC 2 audits. Consultants provide valuable insights, guidance, and an unbiased assessment of your readiness for the audit.
Visit our SOC 2 Compliance Page to understand what our solution entails. We want to be part of your Compliance Team!
Tip 3: Gather And Organize Only the Necessary Documentation
Efficiency is key when preparing for an SOC 2 audit. Avoid drowning in paperwork by focusing on gathering only the necessary and relevant documentation and evidence required for your audit. This approach saves you time and ensures that your efforts are targeted and effective.
Focus on the documents that directly relate to the controls being audited. These may include policies, procedures, security incident reports, system configurations, and evidence of security training.
Compliance Automation Software will be helpful for not only the gathering, but also the organization of your documentation. This software automatically collects evidence and stores all governance, risk, compliance tracking, and policy management in one place for the auditor.
How BEMO Can Help
At BEMO, we understand the challenges of preparing for an SOC 2 audit and embracing a culture of security and compliance readiness. Our team of experts is dedicated to assisting businesses like yours in achieving SOC 2 compliance and maintaining it year-round.
With our guidance and support, you can navigate the complexities of compliance effortlessly and demonstrate your unwavering commitment to safeguarding sensitive data.
We've been there ourselves; BEMO is a verified SOC 2 Compliant Company, therefore we understand how the process is from start to finish and will be thrilled to guide you to success as well!
Contact us today, and let's embark on your journey toward compliance excellence. Your data security and your clients' trust are worth it.
Top 10 Posts
-
Google Workspace to Office 365 Migration: A Step-by-Step Guide
-
Office 365 MFA Setup: Step-by-Step Instructions
-
What is The CIA Triad?
-
CMMC Compliance Timeline: Dates, Deadlines & Phases
-
What is Microsoft Purview ? Your A to Z Guide to Getting Secure Fast
-
When Will CMMC 2.0 Be Required for DoD Contracts?
-
How to Migrate from GoDaddy to Office 365
-
SharePoint vs. OneDrive (What's the Difference Again?)
-
How Much Does ISO/IEC 27001 Lead Auditor Certification Cost in 2025?
-
How to Set Up Office Message Encryption (OME)


Leave us a comment!