
BYOD, or Bring Your Own Device, is a modern workplace concept that's shaking up the traditional office dynamic. It's a simple idea with significant implications: instead of being confined to company-issued devices, you get to bring in your own gadgets – whether it's your laptop, smartphone, tablet, monitor, and so forth– to get the job done.
Now, you might be wondering, why would anyone want to use their personal devices for work? Wouldn’t it be simpler and safer for my company to provide everyone with the same model device?
Well, the reasons are as diverse as the devices themselves, and there are merits and drawbacks to both sides of the debate. For example, this very article you’re currently reading I crafted with my personal computer, mouse, and keyboard, from the research to the drafts and graphics. I designed everything using my corporate credentials and apps but through my laptop.
For me it all boils down to the comfort and familiarity of my own tech setup. I know every nook and cranny of my devices, from the keyboard shortcuts to the quirks of my display. With BYOD, you get to leverage that same sense of familiarity and efficiency in your work environment, making tasks feel like second nature.
Moreover, since the laptop belongs to me, I can take it wherever I go – whether it's working from home, a café, a library, or even while traveling!
But like I said, there are other factors that weigh in when you choose to allow this policy within your company. (We emphasize the word "policy" because it's essential to set clear rules to make sure personal devices are used safely and effectively for work).
Read along to compare both sides to the story and get some best practices for applying BYOD in your work culture.
Table of contents
- Pros and Cons of BYOD
- Checklist to Create a Strong BYOD Policy
- Protect Access to Company Data on Your Personal Devices
Note: check out this other article if you want to compare byod vs corporate device.
Pros and Cons of BYOD
Approaching the topic of Bring Your Own Device (BYOD) isn't as straightforward as seeing it in black or white. As I mentioned in my case, BYOD presents various benefits, but it also brings along its set of challenges. That's why it's crucial to acknowledge the nuances and understand the gray areas.
In this section, we'll delve into the pros and cons of BYOD to explore both sides in detail.
BYOD Details to Consider
Benefits of BYOD:
1) Less Tech Adoption Hassle: When employees use their own devices, they can use features and apps they already know. This makes work easier and faster, and they're less likely to get stuck solving obstacles.
2) No Training Needed: Since employees are already comfortable with their own devices, they don't need extra training to start working. They can get straight to work without any delay.
3) Cost Savings: This approach reduces upfront equipment and training costs and minimizes ongoing expenses related to purchasing and maintaining work devices. The funds can be redirected into other areas, such as business expansion, compliance, improving the digital infrastructure, creating customer loyalty programs, etc.
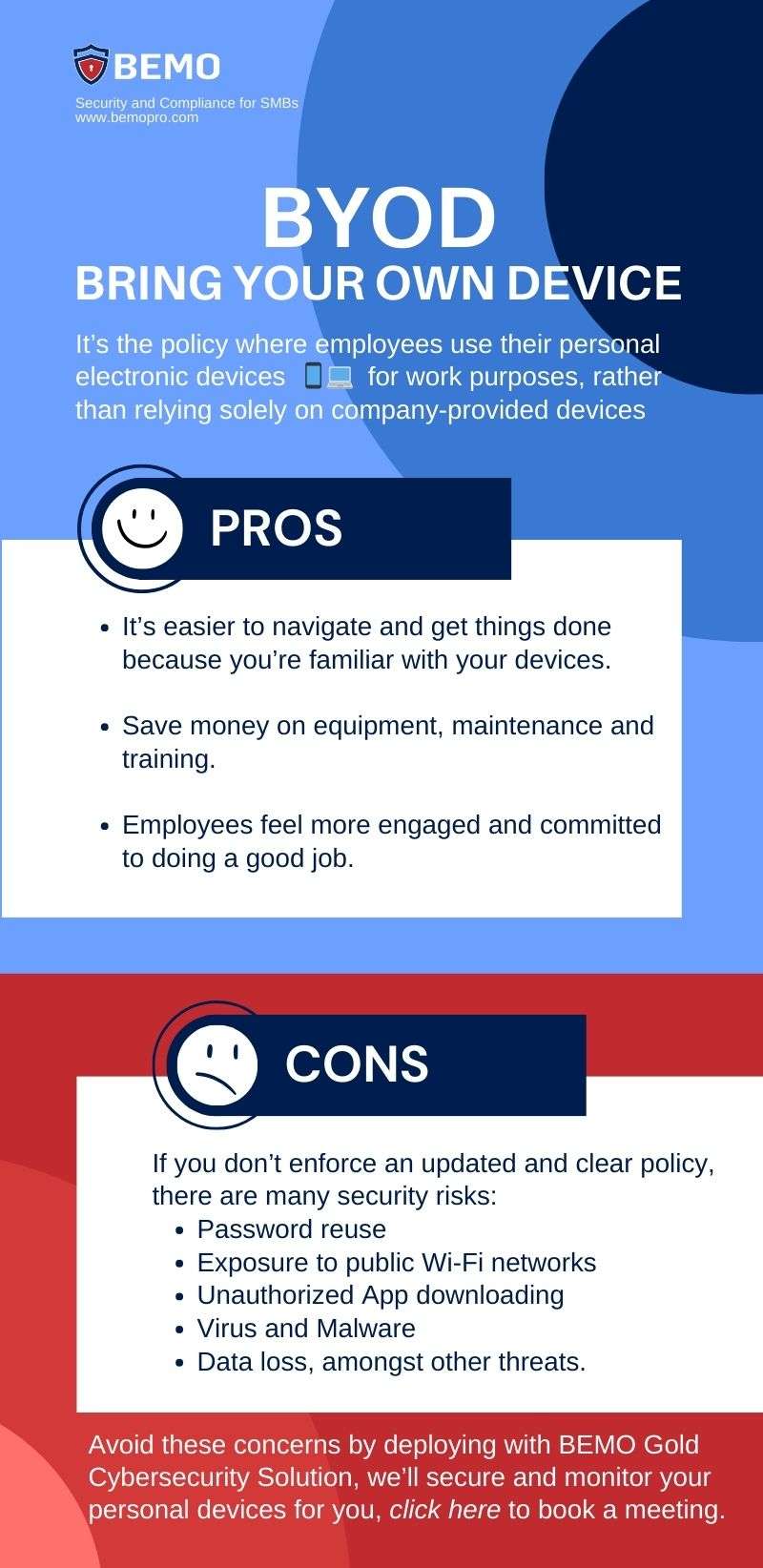
4) Happier Employees: Granting employees the autonomy to use their personal devices fosters a sense of ownership and empowerment in their work. This heightened satisfaction translates into increased engagement, motivation, and overall job satisfaction. Consequently, employees are more likely to demonstrate greater commitment to their roles, leading to enhanced performance and productivity.
Plus, being able to move between different locations without being tethered to specific devices or workstations enhances work-life balance by empowering employees to choose where and when they work most effectively.
Cons of BYOD:
1) Security Concerns: BYOD introduces inherent security risks, as personal devices may lack the robust security measures typically found in corporate-owned devices. Employees may use weak passwords or reuse passwords across multiple accounts, increasing vulnerability to unauthorized access.
Additionally, BYOD devices may connect to unsecured public Wi-Fi networks, exposing sensitive data to potential breaches. Moreover, employees may store confidential company information on personal devices without encryption or adequate safeguards, heightening the risk of data theft, loss, or inadvertent deletion.
2) Support Challenges: Adopting a BYOD policy means possibly making extensive modifications to your existing IT infrastructure and technical support mechanisms to accommodate all the diverse devices and applications.
Just be aware of the logistical challenges for IT departments tasked with ensuring compatibility, security, and support across a myriad of devices and platforms. From troubleshooting software compatibility issues to providing technical assistance for device setup and maintenance, IT teams face heightened demands and complexities in managing a BYOD environment effectively.
Checklist to Create a Strong BYOD Policy
Let’s start with the basics. What is a BYOD Policy?
BYOD policies are a set of rules that govern how employees can use their personal devices for work purposes. Just because people get to use their own devices, doesn’t mean you give up control over your company’s safety and data access management.
The BYOD Policy exists to tackle the Cons listed above. It’s your way to address the support demands and reduce the probability of breaches by strengthening your network.
Here are some things you’ll need to tick off your list before building the policy itself:
- Conduct a risk assessment: Identify the risks associated with using personal devices for work purposes. This will help you determine the appropriate security measures to implement.
- Consult with stakeholders: Involve all relevant stakeholders in the policy-making process. This can include HR, IT, and legal teams.
- Deploy a software application for managing the devices that are connecting to the network.
Now you can start writing the policy to outline both the employer's and the user's responsibilities. To do so, consider these points: 
- Define the purpose of the policy: Explain why the policy is necessary and what it aims to achieve. This will help employees understand the importance of the policy.
- Determine the devices allowed: Specify the types of devices allowed to access the company's network. Specific models may be recommended, or a minimum operating system level could be required based on compatibility with company software and security features.
- Establish security measures: For instance, smartphones and tablets may need to have built-in encryption features enabled to protect data in transit and at rest. Laptops may need to have antivirus software installed and regularly updated to guard against malware and other cyber threats.
- Define acceptable use: Outline the acceptable use of personal devices for work purposes. This can include restrictions on downloading unauthorized apps, accessing restricted websites, and sharing sensitive company information through personal email or messaging platforms. This policy should also include legal clarification on who owns the apps and data and terms for removing access to the data (in the event of a lost or stolen device or when the employee leaves the company).
- Specify the support provided: Explain the level of support employees can expect from the IT department. What will be the right procedure and workflow? This can include help with setting up devices, troubleshooting issues, and providing security updates.
- Communicate and training: Lastly share the policy with everyone affected by it, include a user agreement, acknowledging that they have read and understood the policy and provide training sessions to employees on how to use their personal devices securely. This can include training on password management, data encryption, and safe browsing practices.
Overall, while employees have some flexibility in choosing their devices, it's important to establish guidelines to ensure compatibility, security, and productivity in the workplace. By following these steps and implementing a comprehensive BYOD policy, you can ensure a seamless integration of personal devices into the workplace.
Don’t forget to regularly review and update the policy to ensure that it remains relevant and effective!
Protect Access to Company Data on Personal Devices
Now that you've weighed the pros and cons of BYOD, you may be eager to explore this approach for your business. Step one is defining the policy, but implementing robust security measures, configuring devices and credentials, and keeping them monitored is no small feat.
That's where BEMO's Silver Cybersecurity solution comes in. From deploying app protection policies to security alert monitoring, we handle it all, leaving you free to focus on your business.
Our solution is seamlessly integrated into the Microsoft environment, leveraging Microsoft Intune Mobile Application Management (MAM) to streamline the deployment, monitoring, and security of mobile apps.
With BEMO Silver, we go above and beyond, providing advanced features such as the ability to separate personal and company data and apps on personal devices. This empowers you to enforce restrictions like prohibiting copy and paste of company data, mandating PIN access, and implementing Remote Company Data Wipe capabilities in case of device loss, compromise, or employee offboarding.
Tip: If you’ve chosen to go with BYOD over company-owned devices for use cases like contract employees or shift workers but would like to provide a full Windows Desktop experience on any device, ask us about Windows 365. BEMO Silver security plus Windows 365 provides a flexible, secure, and manageable solution that fits well with the dynamic nature of BYOD environments.
And that’s just on personal devices, we cover email, identity, document, and corporate devices too!
With BEMO's comprehensive approach to secure BYOD, you can confidently embrace the benefits of flexibility and productivity without compromising on security.
Top 10 Posts
-
Google Workspace to Office 365 Migration: A Step-by-Step Guide
-
Office 365 MFA Setup: Step-by-Step Instructions
-
What is The CIA Triad?
-
What is Microsoft Purview ? Your A to Z Guide to Getting Secure Fast
-
CMMC Compliance Timeline: Dates, Deadlines & Phases
-
When Will CMMC 2.0 Be Required for DoD Contracts?
-
How to Migrate from GoDaddy to Office 365
-
SharePoint vs. OneDrive (What's the Difference Again?)
-
How Much Does ISO/IEC 27001 Lead Auditor Certification Cost in 2025?
-
How to Set Up Office Message Encryption (OME)


Leave us a comment!